Third Party Risk Management
Third Parties Risk Management is the Right Practice

The growing demands of compliance and the complexity of related processes ensure that organizations adopt best practices to strengthen security measures. This helps to ensure that vendors working with the organization are adhering to the most current security standards, thereby boosting confidence in business operations.
Customized Reports in Excel and PDF
Download your reports in pdf and excel format, with full customization and maps to compliance reports. Continuous Assessments or 1 time assessments, Department wise vendor assessments, All features in one solution
Third Party Risk Dashboards - Real time on engagement levels
1. Onboard Vendors
2. Assign the security questions
3. Collect Evidence and Measure Security compliances
4. Workflows inbuilt to function as operations
5. Share the Insights

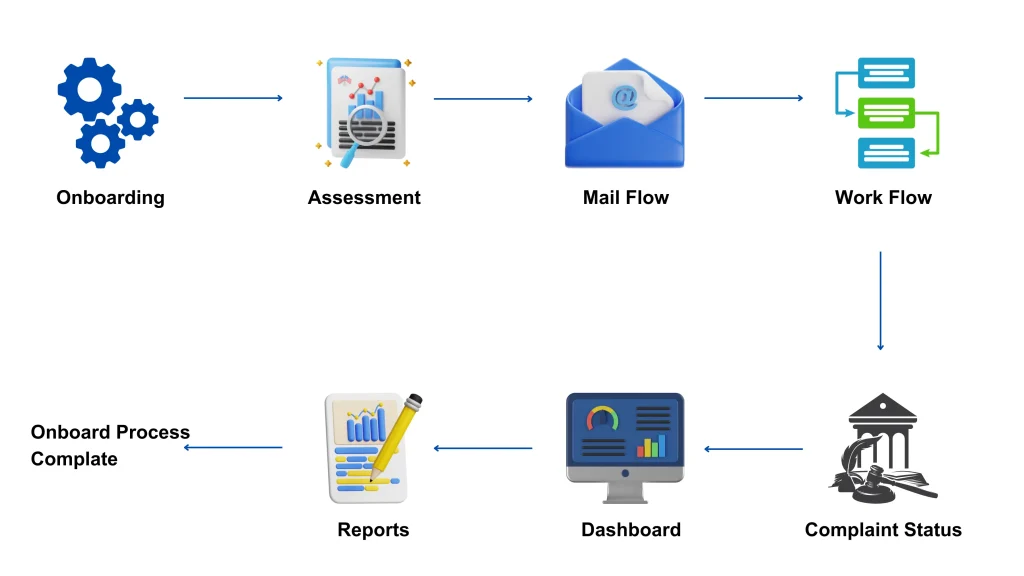
Third Party Risk Management Process Flow

Traditional approach to Third-Party Risk Management tends to be fragmented, with each department handling its own vendors and relying on separate, manual processes for data verification. This method is not only error-prone and time-consuming, but it also often leads to data gaps. Additionally, maintaining a centralized database of third-party information remains a significant challenge. To address this, businesses now require a centralized and automated third-party risk management system to enhance efficiency, accuracy, and security. With a centralized repository, companies can conduct multiple assessments and monitor compliance more easily while ensuring data privacy is upheld.
Availability of the Solution
CONTACT US
- A - 31, Sector - 4 Noida, UP 201301 India
- sales@whitehats.in

